DocuMed is committed to meeting HIPAA (Health Insurance Portability
and Accountability Act) compliance. We remain diligent in our internal
security guidelines and continuously work to achieve the highest security
levels possible. Our focus aims to protect the confidentiality
of all privileged patient and client information stored internally and transferred
over public networks. As part of our total commitment to security and HIPAA,
DocuMed has addressed these key areas:
DocuMed uses the latest technology software to ensure that only authorized users
can access the DocuMed software and website. Each user is
authenticated by a strong userID and password. Information pages are only available to authorized
users and are managed by role-based authentication
procedures. We use firewalls and anti-virus software to block unauthorized access. DocuMed remain diligent
in managing access through business practices that ensure that only current employees
and clients are authorized. Background checks are also conducted
on DocuMed employees and vendors.
DocuMed uses multiple features of Microsoft's ASP.NET Web application architecture
to maximize its security protection efforts. Various approaches to authentication, authorization and secure communication are used throughout your application's multiple tiers to ensure a defensible
security strategy.
The diagram below summarizes the various technologies available by Microsoft together with the primary authentication
and authorization options provided by each one.
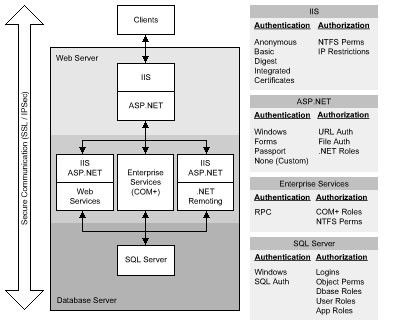
.NET Web Application Security
The DocuMed data center operates in a secure site with on-site security professionals
to monitor physical access to the site 24 x 7. Access to the data center is
through secure card verification. Our security measures include stringent personnel access which subjects
people requesting physical access to multiple levels of identity verification.
To work effectively, IT security must be regarded as an attitude. Providing firewalls and antivirus software
and intrusion detection will only get you so far. DocuMed offers security awareness training to all of its full-time
staff in order to be diligent in avoiding an IT security breach. The weakest
link in a company's defenses is almost always a person rather than a lump of technology.
There's only one way to discover the true state of IT security, and that's to try breaking it. DocuMed
uses automated software products which try to mimic the behavior of a typical hacker.
But the best way to discover the full truth about the state of your security is to undergo a
penetration test which identifies security holes, then plugs them.
Business continuity planning (BCP) help us plan to keep our doors open in the face
of both natural and human-made problems while minimizing the impact of disruptions
on customers and business operations. We start by working with our business unit
managers to prioritize the recovery process with the criticality of the business
function. The planning, testing, and execution of a business continuity plan are
a constant and ongoing effort that has to reflect changes in the makeup of the business
and changes in the threats that the business faces. Here are the steps we have taken:
- We have engaged the services of a site manager to provide backup
of our data center should our primary site become unavailable.
- We have identified high-profile operation functions needed to continue
our business and assigned ownership.
Our goal is to provide near-seamless set of services to the customer and making
sure that the business continues to function in the event of a problem or outage.
|